Professional Portfolio
My Most Recent Experiences
MVG - OATI 2023 - 2025
Cloud / IT support
What did I do?
-
Azure Identity Management
One of my core responsibilities was managing user identity and access through Azure Active Directory. I configured user accounts for new hires, including assigning licenses and setting up permissions across Microsoft 365 services. I also managed SharePoint access and worked with role-based access control to ensure people had access to the right tools without overprovisioning.
This meant learning how Microsoft handles identity and access in a real-world environment and applying those principles daily to maintain both usability and security.
-
Active Directory and Hybrid Infrastructure
We maintained a hybrid environment, so I worked with both on-premises Active Directory and Azure AD. I handled user account creation, password resets, group policy edits, and permission auditing on the on-prem side—while syncing those identities with the cloud using Azure AD Connect.
Understanding how the two environments interact was key—especially when troubleshooting sync issues, managing group memberships, and ensuring users had consistent access no matter where they were connecting from. It gave me hands-on experience with how legacy systems integrate with modern cloud solutions, and how to support both in a production environment.
-
Multi-Factor Authentication Rollout
Security became a growing focus for the team, and I helped implement multi-factor authentication (MFA) across our Office 365 infrastructure. I worked on configuring the rollout through the Microsoft Admin Center, testing various user scenarios, and writing up documentation for onboarding and troubleshooting.
I also supported users during the transition, walking them through mobile app setup and recovery options. The rollout significantly improved our authentication security with minimal disruption to the user experience.
-
Security Monitoring
I assisted in reviewing Active Directory logs and alerts to detect potential security threats. This included tracking failed logins, lockouts, or logins from unusual locations. I collaborated with the team to flag suspicious activity and contributed to documenting response workflows and escalation paths.
This gave me valuable hands-on exposure to incident detection and how support roles play a key part in the larger security picture.
-
How is this relevant to Cybersecurity?
This role helped me build a strong understanding of how identity, access, and security overlap. Working in a hybrid environment showed me how legacy systems and modern cloud platforms can introduce vulnerabilities if they’re not managed carefully. Whether I was managing permissions or digging through logs, I always had to consider the security implications.
Implementing MFA and supporting incident response helped me understand the practical side of layered defense. I saw how quickly something can go wrong—and how important it is to have the right controls in place beforehand.
That experience gave me the foundation to think like a security analyst, even while working in IT support. It pushed me to learn more, dig deeper, and look beyond just keeping systems running—I want to be the one helping protect them too.
MVG - OATI 2019 - 2023
Systems Engineering / Integrations
How did I help?
-
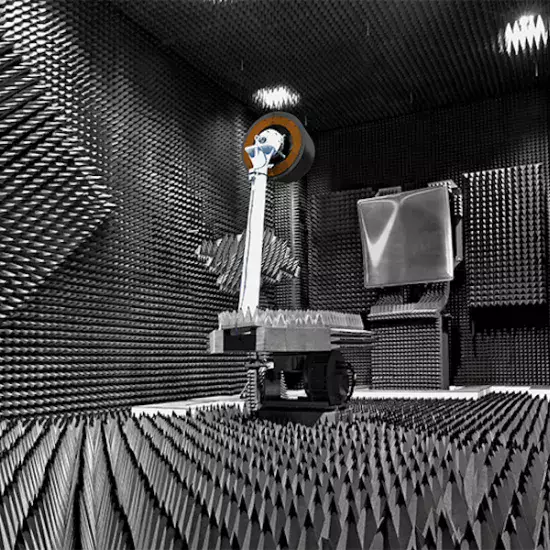
System Design and Integration
I worked my way through the entire engineering life cycle. With my habit of diving into new concepts, I became a key player in several complex systems. These measurement systems weren’t standalone—they relied on lots of supporting subsystems that had to be designed, tested, and integrated onsite at the customer location.
One of my first and most memorable projects involved an IR/thermal camera system. I had to learn how to work with vendors, read compliance docs, and source parts that fit some pretty strict criteria. This system had to handle up to 1000°C, so we needed special lenses and the right internal hardware to match those requirements.
-
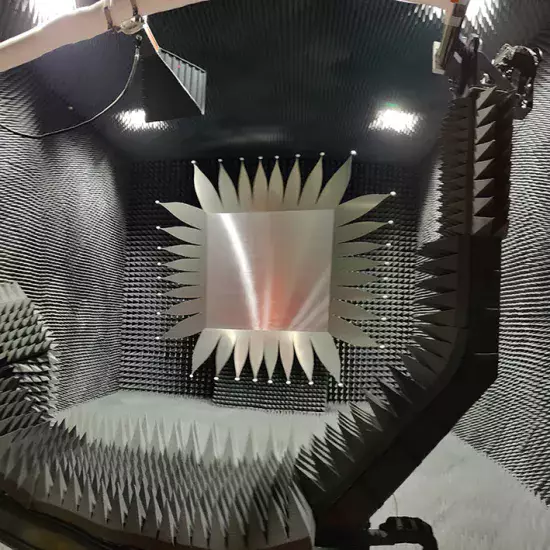
The Thermal System

This setup used four IR cameras and a Modbus PLC. I designed it to run remotely on the internal network so any PC could view the feeds. I had to learn how to set thresholds and create signal flags that triggered warnings—or even the fire suppression system. Since I built it, I also trained the customer on how to use and configure the whole setup.
-
Project Leadership
A lot of my time was spent onsite, working directly with customers. I made sure teams were aligned and had the latest documentation, install manuals, and all the parts they needed. I was involved in test planning and integration, so I had to stay on top of everything to keep the project moving.
-
CCTV and Thermocouple Integration

One big project had a major milestone—getting all the subsystems installed, tested, and signed off by the customer. That’s harder than it sounds. I put together a detailed install plan with cable routes and labeling instructions.
Another team handled the CCTV cameras, while I worked with a colleague to install the thermocouple system. I coordinated with installers, mechanical engineers, and integration teams to make sure everything I designed and tested was installed correctly.
-
Process Optimization
I built documentation that made life easier for the whole engineering team. Systems integration means working across disciplines every day, and for one of our biggest jobs, I created what we started calling the “Mega Excel Sheet.”
The Mega Excel Sheet
I’m not going to go deep into Excel—but I did end up with the most viewed document on our SharePoint. I took a complicated system with thousands of connections and turned it into a simple, searchable sheet. Every connection was documented: cable name, type, connector ends, and where it was terminated—panel or endpoint.
From there, I created pivot tables to help with BOM deployment. Mechanical engineers used it to figure out panel layouts. RF teams used it to plan cable routes. It took more work up front, but it supported the whole project from start to finish.
-
How is this relevant to Security?
When you’ve spent months building and integrating systems, you learn how important it is to protect them. Whether it’s hardware, code, or process—there’s always something worth securing. I’ve had to think about what happens if things go wrong or someone pushes the wrong button.
I’m always learning and solving weird problems, and that mindset fits right into cybersecurity. I’m not afraid of jumping into the unknown, breaking something, and figuring out how to fix it. That’s how I work best.
Security feels like the next step—a space where I can use everything I’ve learned so far, keep pushing myself, and work on problems that really matter. I’m excited to be part of it.
CTDI 2015 - 2019
RF Technician
How did I improve?
-
Custom C# Tool for Metadata Modification
I taught myself C# to solve a bottleneck in our radio board workflow. We had a batch of outdated boards that required manual metadata modification—a process that took about two hours per board. I created a custom program that automated this task, significantly cutting down the time required per board.
This tool not only saved us hours of repetitive work but also helped bring a large batch of old radios back into service—radios that otherwise would have stayed shelved. It was a practical solution that came from seeing a problem, diving into the unknown, and building exactly what we needed.
-
RF System Troubleshooting & Board Repair
On top of software fixes, I also worked hands-on with hardware. I performed detailed component-level troubleshooting and modifications on complex RF systems. This included reprogramming and repairing FPGA boards, radios, and amplifiers.
It was deep-dive work—scoping signals, tracking down faults, and making changes directly to hardware. Every board was a new challenge, and I enjoyed the process of working through each issue until the systems were running reliably again.
-
How is this relevant to Cybersecurity?
Learning C# to build a custom tool from scratch gave me a strong sense of how powerful code can be when it’s solving real problems. That mindset—figuring out how systems work, spotting inefficiencies, and building your own solutions—is essential in cybersecurity.
Working with radios, FPGAs, and low-level systems also taught me how vulnerable embedded systems can be if they aren’t properly protected. Whether it’s firmware, hardware, or the tools that manage them—there’s always a security angle. This experience pushed me to think more critically about how devices can be manipulated.